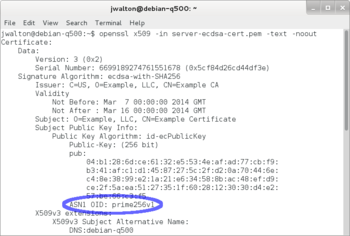
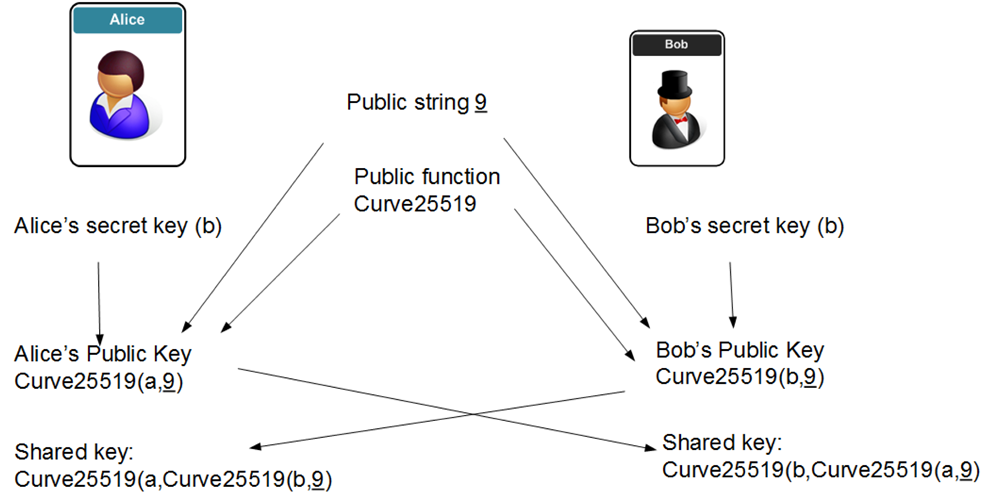
The Security Buddy on Twitter: "How does Elliptic Curve Cryptography work? https://t.co/f6k3Mbb0ls #security #encryption #ECDH https://t.co/z6uYu73g32" / Twitter
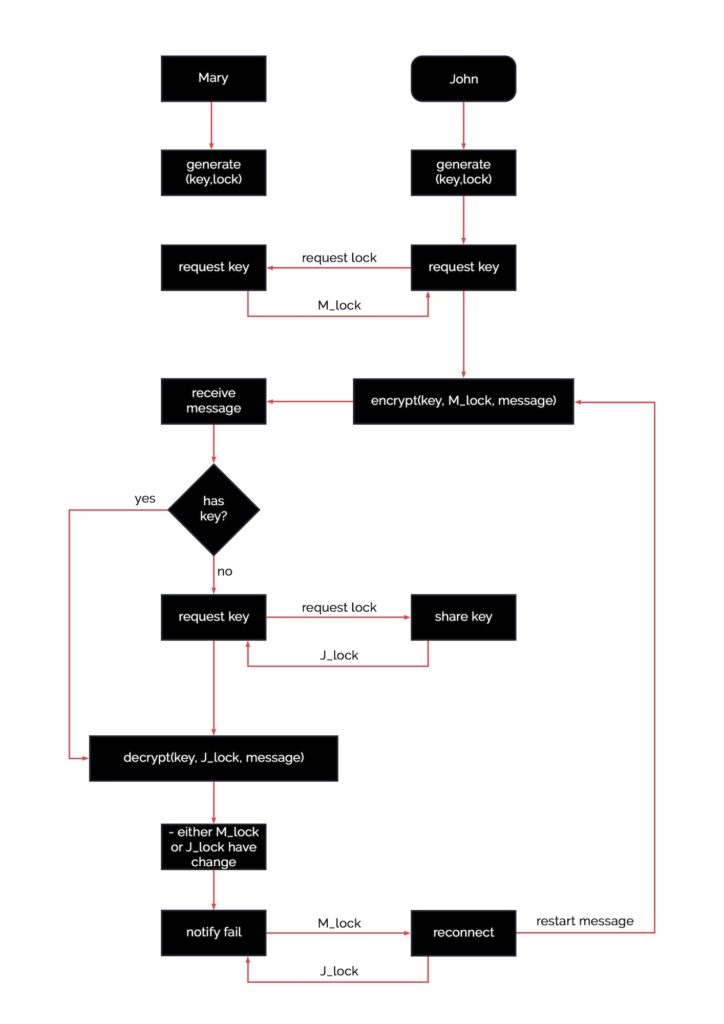
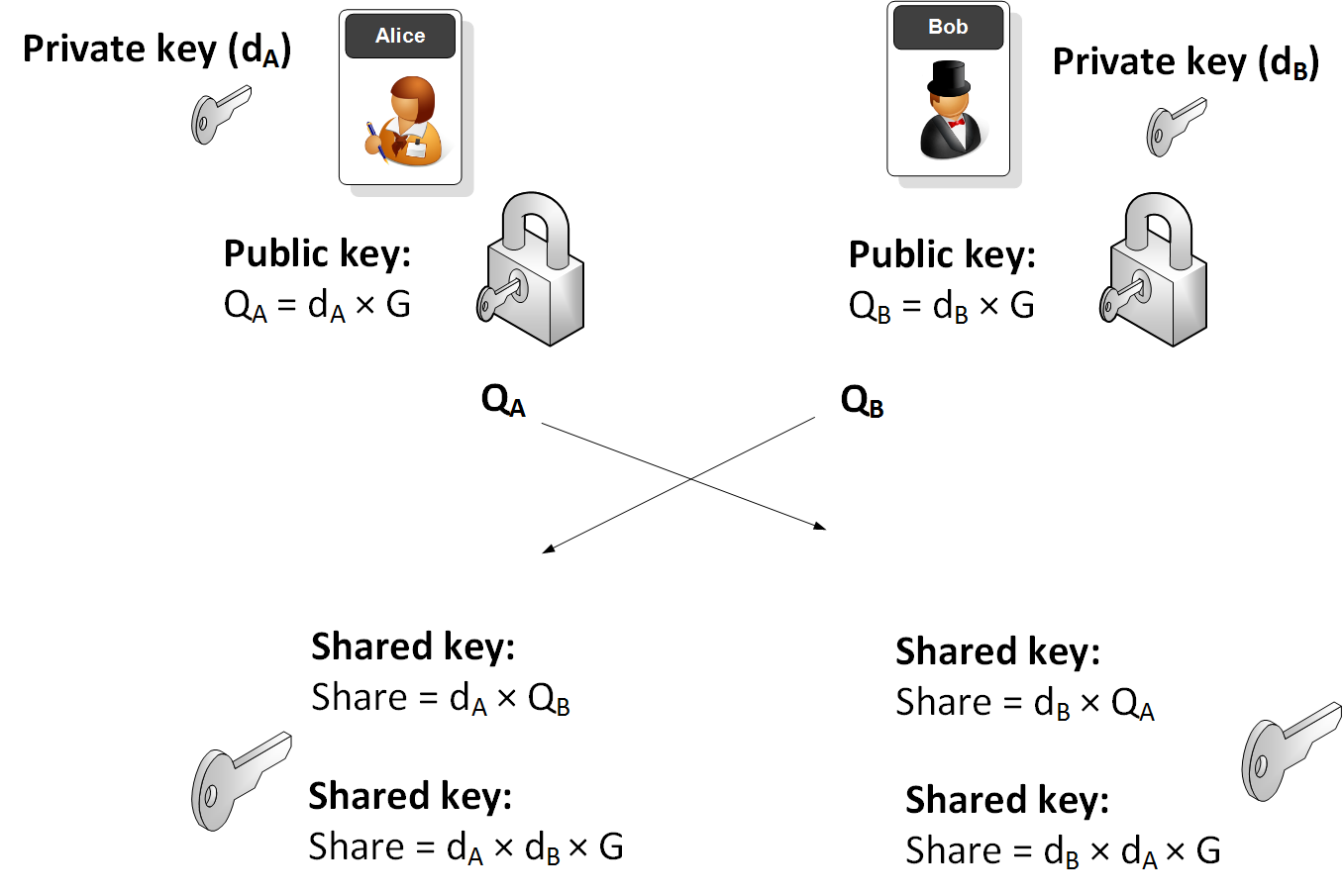
GitHub - jeswinMathai/SC-ECDH: Secure Communication System using Elleptic Curve Diffie Hellman Algorithm
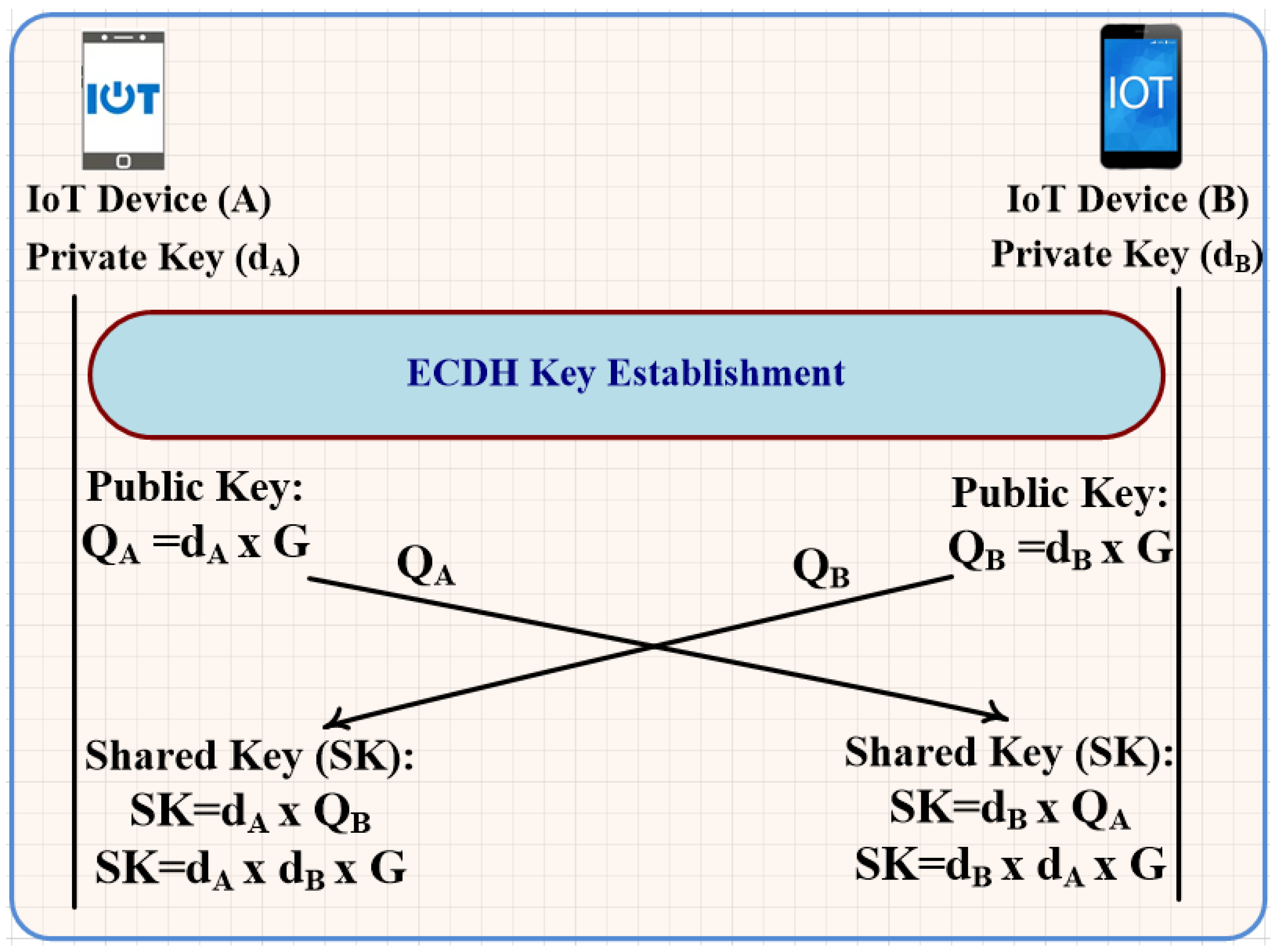
Processes | Free Full-Text | Unforgeable Digital Signature Integrated into Lightweight Encryption Based on Effective ECDH for Cybersecurity Mechanism in Internet of Things




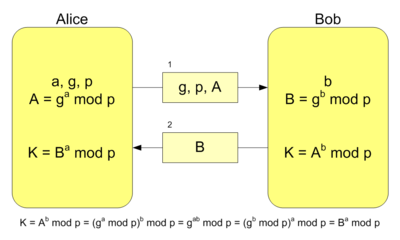



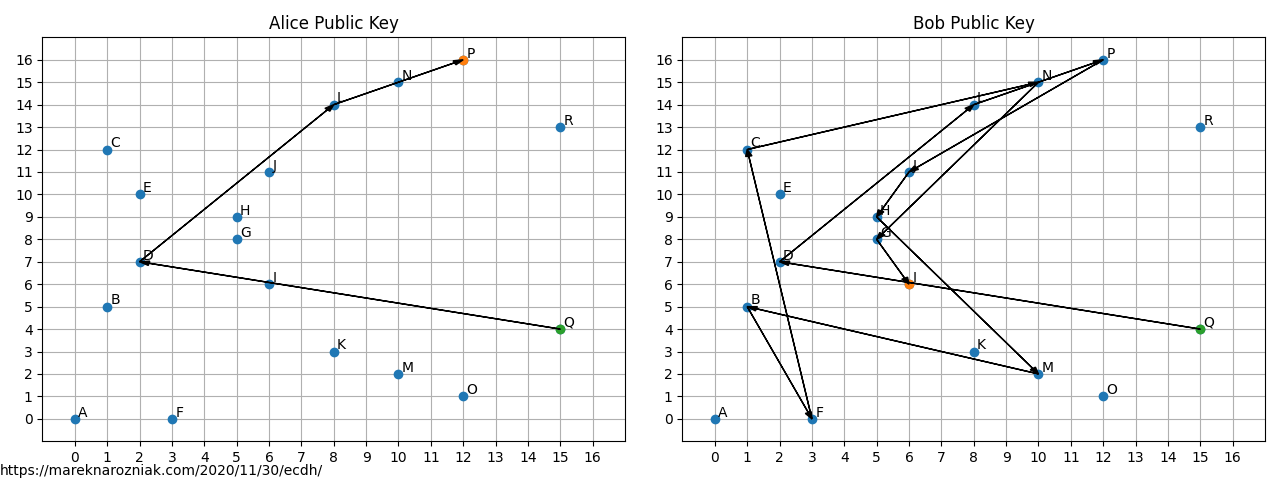
![PDF] The Elliptic Curve Diffie-Hellman (ECDH) | Semantic Scholar PDF] The Elliptic Curve Diffie-Hellman (ECDH) | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/de032e79b6116aeb3efc26de258903d6fdc24a08/1-Figure1-1.png)